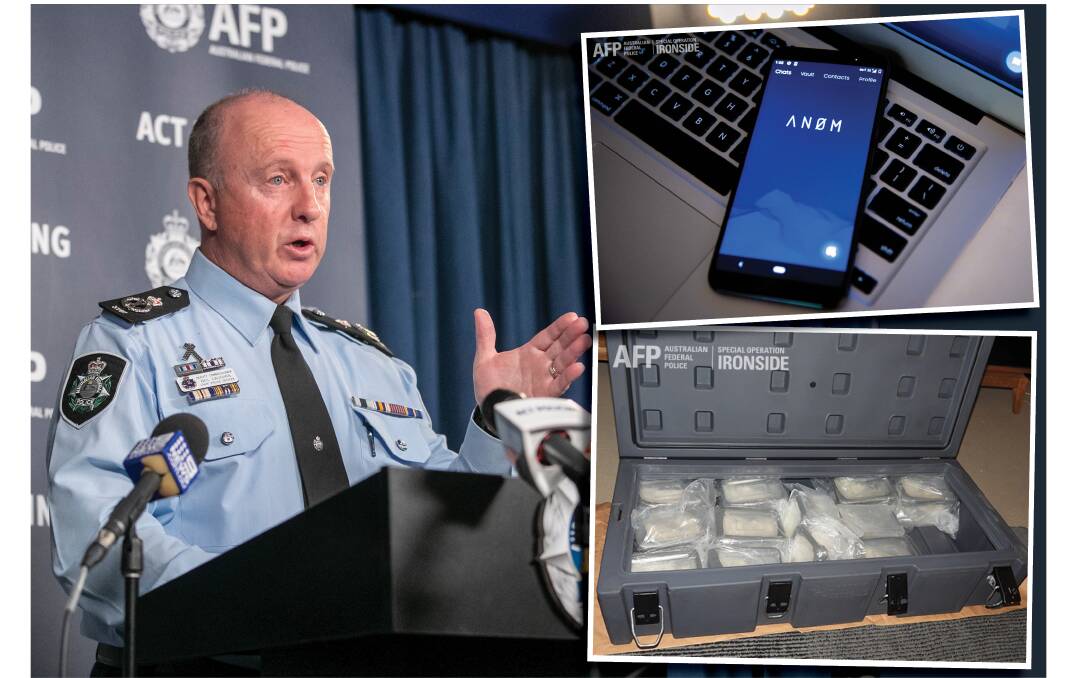
Old-fashioned forms of police investigation and human source networking must now be relied upon as criminals ditch their now-compromised encrypted phones in the wake of Operation Ironside's massive national drug syndicate busts, over 280 people have been charged.
Subscribe now for unlimited access.
$0/
(min cost $0)
or signup to continue reading
ACT Chief Police Officer Neil Gaughan said "that one of the challenges we have [as police] is that we are now going back to utilising human sources to find out what's going on because we haven't got any ears on [the criminals]".
The ears to which he referred were those at the heart of Operation Ironside, which reached its "resolution" phase last week.
Deputy Commissioner Gaughan is perfectly placed to know the Ironside operational detail intimately. Three years ago and one rung below the chain of command where he now sits, he was the federal police Assistant Commissioner in charge of Organised Crime while the operation was in its very infancy.
He helped to knit the Australian end of the now-infamous operation together and set up the resources within the Edmund Barton Building - including a windowless "bunker" room - as a safe room while the Australian arm of the covert surveillance was set in motion.

For three long years the extraordinary multinational-technology project was a tightly held secret within the Australian Federal Police, with Deputy Commissioner Gaughan one of a handful of people holding the keys to the secret.
"It [the operation] was kept pretty tight within the AFP for a considerable period," CPO Gaughan said.
At the very core of the operation was the knowledge and belief that criminal networks had built a huge dependence on a trusted and highly encrypted communication system to manage their everyday business of obtaining and distributing illicit drugs.
When the previous and much-used encrypted technology known as Phantom Secure was compromised and the company's chief executive, Victor Ramos, jailed for nine years, the opportunity arose for a mechanism to replace it.

With Ramos and Phantom Secure gone, authorities audaciously sought to fill the gap, devising a cunning plan whereby it would develop a platform and allow criminal "influencers" to disseminate it. The device was an encrypted Google Pixel cell phone, stripped to contain a special app called AN0M.
The offenders who used the encrypted phones did so believing their communications were completely secure.
But the reality was completely different. Behind the scenes, federal agents in Australia and the US were recording every exchange and waiting for the moment to pull the rug out from under hundreds of illicit drug networks, including outlaw motorcycle gangs, and Asian drug syndicates.
"Once Phantom Secure was taken down, there was always a discussion at the operational level to determine 'where to from here, what do we do next, how to we try to maintain coverage on these crooks?'," Deputy Commissioner Gaughan said.
"There was a lot of work undertaken at the investigator level to see how these things could happen."
READ MORE:
A comprehensive affidavit in support of a search warrant, filed in the US District Court in California and publicly unsealed on June 7, was one of the triggers for law enforcement to pounce.
The document presents a fascinating insight into the 2018 genesis of the idea through a first-hand account from FBI special Agent Nicholas Cheviron, based out of San Diego.

"Because hardened encrypted devices provide an impenetrable shield against law enforcement and detection, it is a service in high demand by transnational crime organisations," Cheviron said in his affidavit.
He detailed how an FBI confidential human source had been developing a "next generation" encrypted communications project.
This informant, with previous convictions and time served for importing narcotics, had worked with the FBI on this program since 2018 in exchange for the possibility of a reduced sentence. Such is the affidavit's level of detail, it also revealed how the source was paid US$120,000 for his services and $59,508 for living and travel expenses.
His product was called AN0M and the FBI then opened its new covert investigation, Operation Trojan Shield, "which centred on exploiting AN0M by inserting it into criminal networks and working with international partners, including the Australian Federal Police, to monitor the communications". In 2018, the FBI offered its devices to three former Phantom Secure "distributors" with "connections to criminal organisations, primarily in Australia".
"These three individuals, relying on their expertise from distributing Phantom [Secure] and seeing a huge payday, agreed," he said.
Australia was the "beta test", with the AFP "obtaining a court order to monitor the devices", Cheviron stated.
One drug import kingpin badly caught up in the police sting was Joseph Hakin Ayik, a former Comanchero bikie who fled the country in 2010 for Turkey to avoid being collared in a $230 million heroin bust.
"Once Hakin Ayik had decided it [AN0M] was the bees knees, it was inevitable there was going to be trust in the system because he's a pretty influential organised crime figure," Deputy Commissioner Gaughan said.
Ayik's once-close connections, via the app, to his former bikie gang mates back in Australia are rapidly unravelling with a former Comanchero Sergeant-at-Arms on the NSW South Coast arrested last week.
Our journalists work hard to provide local, up-to-date news to the community. This is how you can continue to access our trusted content:
- Bookmark canberratimes.com.au
- Download our app
- Make sure you are signed up for our breaking and regular headlines newsletters
- Follow us on Twitter
- Follow us on Instagram

